Over the past ten years, the Dark Web has earned an unsavoury reputation. Known as a place synonymous with drugs, weapons, illicit pornography and stolen data. 2013 saw the arrest and conviction of Ross Ulbricht, an American computer programmer and mastermind behind Silk Road. As a result, worldwide attention was drawn to the Dark Web. But what is it? And what threat does it pose to your business?
What is the Dark Web and how is it accessed?
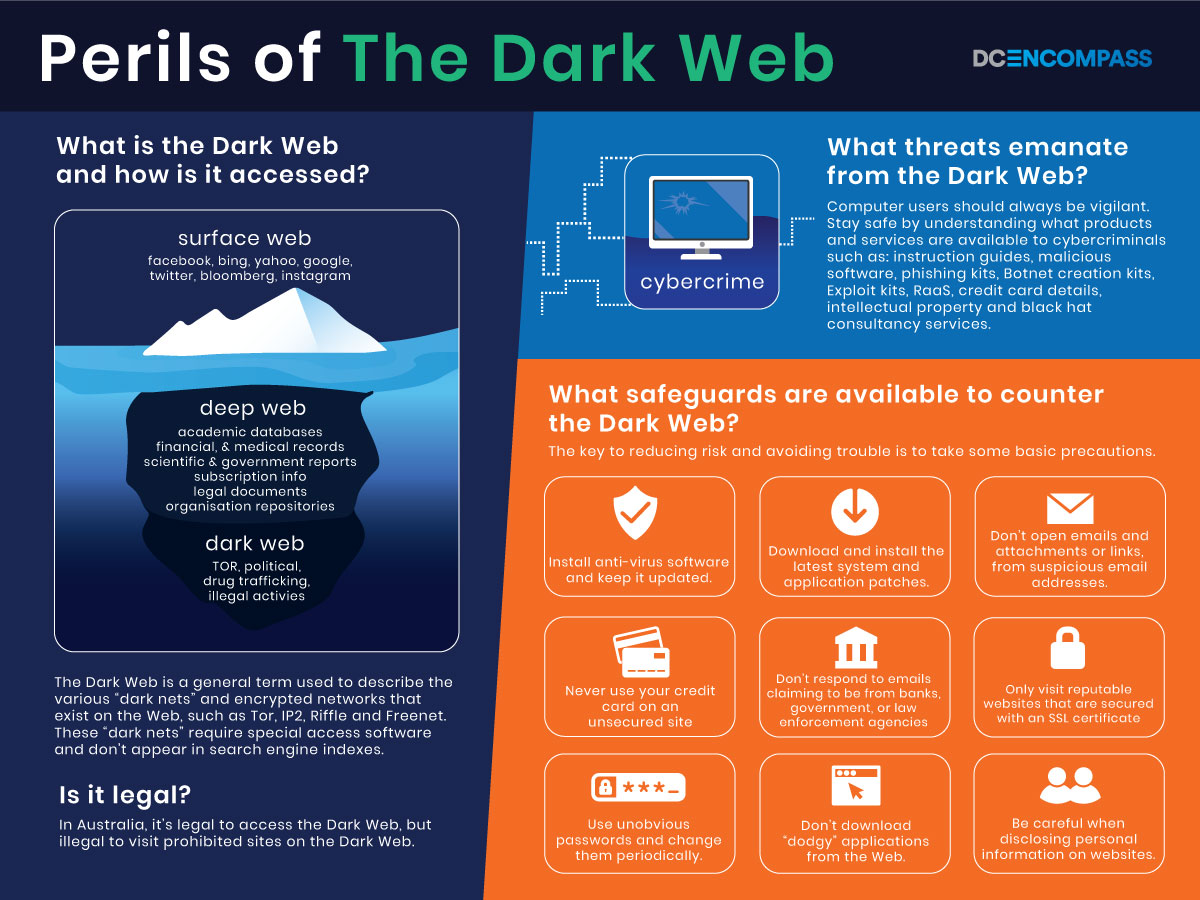
In short, the Dark Web is a general term used to describe the various “dark nets” and encrypted networks that exist on the Web. For example, Tor, IP2, Riffle and Freenet. These “dark nets” require special access software. They also don’t appear in the indexes of search engines like Google and Bing. Collectively, these “dark nets” are a treasure trove of confidential data and malicious software. All of it for sale.
A good example of a Dark Web horror story is the Ashley Madison case. In 2015, extramarital dating site Ashley Madison failed to meet the demands of a vigilante group. Consequently, it had its user database posted on the Tor “dark net”. The data breach embarrassed millions of people. As a result, it cost Ashley Madison $11.2 million in client settlements.*
The best-known “dark net” network is Tor. Also known as The Onion Router. Tor Project, an American not-for-profit organisation dedicated to web privacy, administers this. The Tor browser and network are free to use. Tor users are able to access any website with a “.onion” suffix.
Tor newcomers usually start off by visiting a directory service. For instance, The Hidden Wiki. The benefit of using a directory service is that it reduces the likelihood of stumbling upon illegal content. Not all websites and activities on the Dark Web are sinister or illegal. There are many legitimate discussion forums and special interest sites.
Graphical Overview
What are the chances of my business data appearing on the Dark Web?
Whilst cybercriminals and hackers are cunning people, they rely to some extent on human apathy and impatience. A business that doesn’t use anti-virus software or download the latest patches is more likely to be attacked. Similarly, is a user who automatically opens every new email and attachment.
The key to reducing risk and avoiding trouble is to take some basic precautions. Examples include:
- Installing anti-virus software and keeping it updated. For organisations running a network, install a firewall as well as implement content filtering. Providing VPN access for remote users can also reduce risk.
- Download and install the latest system. As well as application patches.
- Don’t open emails and attachments, nor click on links, from unknown or suspicious email addresses.
- Never use your credit card on an unsecured site.
- Don’t respond to emails claiming to be from banks, government departments and law enforcement agencies. Instead, phone them.
- Only visit reputable websites that are secured with an SSL certificate.
- Use unobvious passwords and change them periodically.
- Don’t download “dodgy” applications from the Web.
- Be careful when disclosing personal information on websites. Preferably, avoid if possible.
Although one’s online safety can never be guaranteed, a business can mitigate risk by making itself a smaller target.
Which tools and resources on the Dark Web threaten my business?
Despite the best efforts of law enforcement and cybersecurity experts to defuse threats, businesses need to remain vigilant. In order to stay safe, it’s worth understanding what products and services are available to cybercriminals on the Dark Web.
- Step-by-step instruction guides for every cybercrime imaginable.
- Malicious software (malware). For example viruses, worms, Trojans, keyloggers, spyware and ransomware.
- Phishing kits. Including authentic-looking templates.
- Botnet creation kits for DDos attacks.
- Exploit kits.
- Ransom-as-a-Service (RaaS). Whereby the command-and-control server is hosted in a “dark net”
- Databases containing sensitive information. For example, personal details, financial transactions and logins/passwords.
- Credit card details.
- Intellectual property. For example, proprietary source code and technical diagrams
- Black hat consultancy services.
Is it legal to access the Dark Web?
In Australia, it’s legal to access the Dark Web. However, it is illegal to visit prohibited sites on the Dark Web. Consequently, the Dark Web should be avoided. Tools like Tor provide users with a certain level of anonymity. Yet, skilled hackers are capable of “de-anonymizing” users very quickly. Curiosity seekers should always take additional precautions when accessing the Dark Web. For example, using a VPN,
Conclusion
In conclusion, there’s little doubt that the Dark Web and its criminal operatives are here to stay. With 11% of businesses reported internet security incidents or breaches in 2017-18*. It is clear that Cybercrime is on the rise in Australia. As such, businesses need to take precautions and remain vigilant. DC Encompass provides a range of proactive and reactive cyber security solutions. Ensuring brand protection and peace-of-mind. Contact us today to discuss your business’s IT Security.