Unlock IT Insights for Business Growth
Stay ahead with expert advice on Managed IT, Cybersecurity, and Unified Communications to scale your business with confidence.
Unlock IT Insights, Managed IT Services, and Cybersecurity Strategies for Business Growth
At DC Encompass, we specialize in providing expert IT insights on Managed IT to help businesses scale efficiently and securely. With cutting-edge strategies, we empower organizations to grow while ensuring their IT infrastructure remains robust and secure. By staying ahead of trends in Managed IT, Cybersecurity, and Unified Communications, we help your business navigate the evolving tech landscape with confidence.
Through expert guidance and reliable Managed IT services, businesses can access the necessary tools to drive growth and success. Our insights on Managed IT ensure your company is well-positioned to scale.
How to Prevent Data Breaches in Your Australian Business: Proactive Strategies That Work
How SMEs Can Prevent Data Breaches in Australian Business In today’s fast-paced digital economy, preventing data breaches in Australian business is more than a best practice. It is a critical survival tactic. Australian SMEs are under constant...
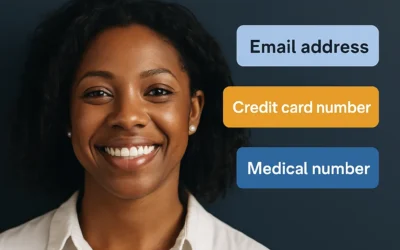
How to Protect Personal Identifiable Information (PII) in Australian Businesses
Why PII Protection Matters for Australian Businesses Personal Identifiable Information (PII) includes any data that can identify an individual, such as names, addresses, tax file numbers, Medicare details, and even IP addresses. In Australia,...
What to Do After a Data Breach: A Step-by-Step Action Plan for Australian SMEs
Urgent First Steps for Australian SMEs Following Data Breach Laws in Australia Australian small and medium-sized enterprises (SMEs) must act immediately when a data breach occurs. The financial, legal, and reputational risks are substantial....
How to Comply with Data Breach Laws in Australia: A Guide for SMEs
Introduction to Data Breach Laws in Australia In today's digital-first business world, data breaches aren't just an IT problem. They are a significant threat to brand trust, customer retention, and regulatory compliance. For small to medium-sized...
Real SME Success Stories: How Australian Small Businesses Transformed with Custom IT
SME IT success stories demonstrate the transformational power of technology for small and medium-sized businesses (SMEs) and not-for-profit organisations (NFPs). Across Australia, organisations that invest in tailored IT solutions are growing...
Managed IT vs In-House for SMEs: Making the Right Choice
Managed IT vs In-House for SMEs is one of the most important decisions growing businesses face today. As technology becomes increasingly critical to every business operation, choosing the right IT management approach can have a direct impact on...
IT Security Essentials for Australian SMEs: Protecting Your Business Without Breaking the Bank
IT security essentials for Australian SMEs are critical today. In a fast-evolving digital world, small and medium-sized businesses face increasing cyber threats. Attackers no longer focus solely on large corporations. SMEs are now prime targets due...
Scalable IT Infrastructure: Growing Your Technology With Your Business
Scalable IT infrastructure for SMEs is no longer optional. In today's fast-paced business environment, small and medium-sized enterprises (SMEs) need flexible, scalable technology to support expansion, innovation, and competitiveness. Without the...
Cloud Solutions for SMEs: Reducing Infrastructure Costs While Maximizing Flexibility
Cloud solutions for SMEs are no longer a luxury. They are a smart, essential investment for businesses looking to reduce IT costs, improve flexibility, and support future growth. Small and medium-sized enterprises (SMEs) face constant pressure to...
Affordable IT Infrastructure Solutions for Small Businesses
Affordable IT Infrastructure Solutions for Small Businesses are essential for staying competitive and resilient in today’s fast-paced economy. Affordable does not mean cutting corners. It means making smart investments that drive business growth,...
The Definitive Guide to IT Risk Management in 2025
Why IT Risk Management Is Critical in 2025 In 2025, effective IT risk management strategies will be critical for safeguarding organizations against evolving cyber threats. As businesses increasingly rely on digital infrastructure, the risks from...
Why You Should Switch to Internet Phone Service for Your Business Today
Introduction to Internet Phone Services If you're looking to improve flexibility, reduce costs, and modernise communication, now is the time to switch to internet phone service for your business. As more organisations across Australia embrace...
Make Your Windows 11 Upgrade Easy: A Stress-Free Guide for Australian SMEs
Make your Windows 11 upgrade easy with this stress-free guide tailored specifically for Australian small to medium-sized enterprises (SMEs) This Windows 11 upgrade for SMEs ensures a secure, smooth transition. Since its release in 2015, Windows 10...
Unlocking AI Potential: How SMEs Can Enhance Data Privacy with Private AI Solutions
Introduction In today's digital landscape, small and medium-sized enterprises (SMEs) handle increasing amounts of sensitive data, from customer information to proprietary business insights. While Artificial Intelligence (AI) offers transformative...
The Ultimate Guide to Managed IT Services for Sydney SMEs
Why Managed IT Services Sydney Are Essential for SMEs In today’s hyper-connected digital world, small and medium-sized enterprises (SMEs) face mounting technological challenges. From cybersecurity threats to evolving customer expectations, staying...
The Ultimate Checklist for Unified Communications (UC) Buyers
Unified Communications Checklist: Bridge Gaps & Scale Unified Communications (UC) plays a vital role in addressing communication inefficiencies while enabling business growth. Whether you're transitioning to remote work, seeking cost-effective...
Technology Tips for launching a successful Startup
Are you starting a new business? If you are a startup business, it is important to think about the product, marketing, and sales. You also need to know what technology can help your company. Here are some technology tips for startups with different...
Role of Human Error: Cyber Security Breaches
Cyber Security Services Cyberspace has grown to be a super-platform for businesses and establishments to thrive. This is because it makes branding and marketing easier, and helps you keep an eye on what is being said about your business. However,...
Endpoint Security Services
With the increased complexity of operations and computing environment in various organizations comes the need for extended security requirements. Endpoint security is one of such solutions designed to meet complex security needs while optimizing...
The Complete Guide to Managed IT Services: Boost Efficiency, Save Costs, and Scale Your Business
The Complete Guide to Managed IT Services for Small Businesses In today’s fast-paced digital landscape, small businesses need reliable technology solutions to stay competitive. Managing IT in-house can be costly, time-consuming, and complex,...
Cybersecurity Ethics
Cybersecurity Ethics play a big part in any field of work, especially in professions that affect the lives of others. Physicians, attorneys, and other professionals have ethics that guide their conduct when they face issues peculiar to their...
Everything To Know About Cloud Computing
Although the term 'cloud computing' has become a buzzword, many people don't yet know what it is and why it is an inevitable shift for organisations aiming for success and profitability within the Digital Era. In this guide, you will learn...
Everything You Need To Know About Application Migration
Application Migration is the process of transferring an existing software application from its computing environment or existing location to another one. These computing environments include laptops, servers, data centers, scanners, printers,...
Enterprise Backup Strategy Best Practices
What is enterprise backup? Enterprise Backup is a computer process that makes copies of system or company data to cover for in case of unwanted incidence of data loss. Nowadays, there are already several methods of backing up data. And, as...
Cyber security challenges in the education industry
Education, particularly post-secondary education, is an important sector in the Australian economy. It is also an incredibly liable and easily-identifiable cyber criminals. Ensuring the cybersecurity of educational...
For more advice on IT trends, cybersecurity news, and issues, contact us for more information.